Click here if you want to read the short version: a Q&A summary of what happened.
Those of you using Chrome, and I understand some of you using Firefox, were unable to access this website because of Google misidentifying it as distributing malware.
As those who know this publication realize, Lucire would never do that and that readers should ignore such warnings.
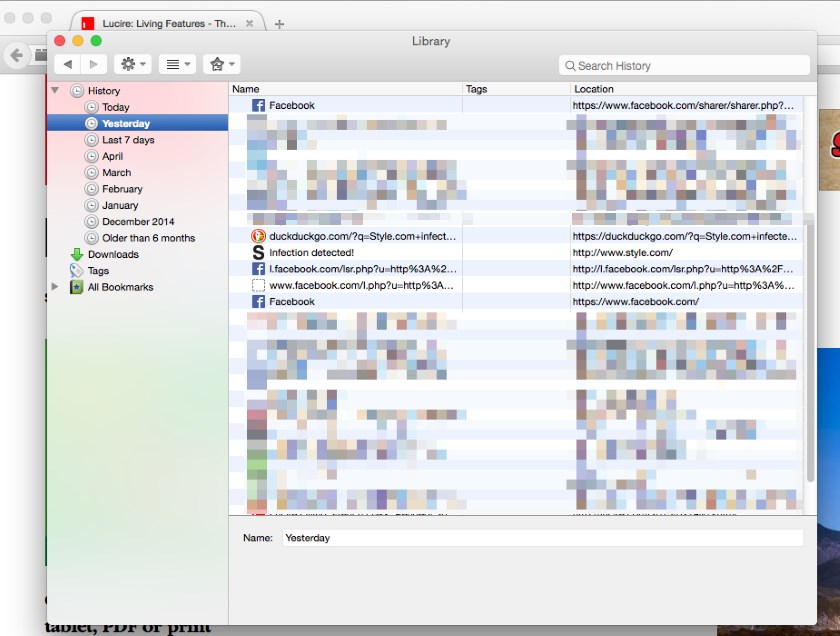
What I can tell you is that on Saturday morning, New Zealand time, we were hacked. Hackers put code in to our ad server and, curiously, the code has Google’s name all over it. I haven’t had confirmation of this, but it could be Google Adsense code. I’ve posted the code at this page and you can view it in a screen shot here. That code linked to another site that they hacked, which did distribute malware unknowingly.
We found this, and deleted all the injected code as soon as possible—in our case, this took place within hours. We did this manually, literally going through every ad entry on our server. After a few more hours, our web experts had deleted every change the hackers made to our advertising server back-end, and locked it down. And, rightly, Google cleared our ad server of any problems.
Strangely, however, Google refused to clear any site that used our ad server, even though none of them were distributing any malware, or linked to any site distributing malware. Google labelled all of them ‘attack sites’. This is, of course, highly damaging to our reputation. For days, Google continued to misidentify clean code linking to a clean ad server as malicious. The great irony is that a lot of this clean code links to Google’s own Doubleclick banners.
It’s sad to say, but this is typical of our experience of Google. Once I helped a friend get his blog back but instead of the 48 hours Google promised, it took six months of a lot of arguing and the intervention of Blogger’s product manager. We’ve uncovered privacy blunders with its advertising network on behalf of netizens. If you were an Iphone user who opted out of Safari’s tracking, Google found a way around it, so we know it has some really strange ideas of what constitutes malware (if they engage in it, it’s OK). Their detection systems should be better, and people expect them to be excellent because it’s a multi-million-dollar firm. Unfortunately, this experience reminds us that they aren’t perfect, and somewhat hypocritical—and that honest folks can get hurt sometimes.
We even went to Google Plus to tell readers, but we discovered today that that status vanished from people’s feeds and from our Google Plus page (though we can still see it). It appears that you aren’t allowed to criticize Google on Google Plus.
I wouldn’t be publishing a statement about this if I didn’t have my facts straight. Today, out of frustration, I went to a forum dealing with badware, called Badware Busters. An expert in the area, Dr Anirban Banerjee, told me that Google can make these mistakes. Even though you have done everything and cleaned up your sites, Google can keep identifying a clean site as malicious. He suggests we remove all our ad server code from our websites for a few days, get the all-clear, and then put things back to normal. We followed that advice today, and I hope that the block will be lifted shortly. [PS.: After a manual review, StopBadware.org cleared Lucire after this post was originally published.]
Or, as I said on my blog today: ‘there may be a drunk driver swerving left and right at the wheel of the Google truck, so it’s your job to make sure that you build a nice road in front for them, rather than insist that they clean up their act and stay on the road.’
We apologize to readers for any inconvenience, especially if you were put off by the false warnings. Rest assured that apart from a brief moment on Saturday morning, this site is secure and your surfing would not have resulted in any harm to your computers. We surf it, too, and we see the same version of the site as you do, so we want things to work properly. We might not be as big as Google, but we do have good systems, and our readers’ best interests at heart.—Jack Yan, Publisher
You can follow a bit more about this saga as it unfolded on Jack Yan’s blog.